JWT Authentication in Node.js Explained Simply
Understanding JWT authentication, token flow, and protected routes in Node.js applications.
If you have started backend development recently, chances are you’ve heard terms like authentication, tokens, JWT, protected routes, and authorization being used everywhere. Initially, all of this can feel slightly confusing because authentication systems involve many moving parts together. But honestly, once the core idea behind JWT becomes clear, the entire flow starts making much more sense.
Authentication is one of the most important parts of backend development because applications need a way to identify users securely. Whether it’s social media platforms, banking apps, e-commerce websites, or streaming services, almost every application needs some form of authentication system so users can log in and access their own data securely.
In this blog, we’ll understand what authentication actually means, what JWT is, how JWT-based login works, the structure of a JWT token, how tokens are sent with requests, and how protected routes work in Node.js applications.
What Authentication Actually Means
Authentication simply means verifying whether a user is genuinely who they claim to be.
For example, when you enter your email and password on a website, the backend checks whether those credentials are correct or not. If they are correct, the server identifies you as a valid user and allows access to protected resources.
Without authentication, applications would have no proper way to differentiate between users. Anyone could access anyone’s private information, which would obviously become a huge security problem.
Why Authentication is Required
Imagine platforms like Instagram, Netflix, or Gmail without authentication. Every user’s private data would become publicly accessible. Authentication exists to prevent that situation.
Applications need a way to:
Identify users
Verify login credentials
Protect private routes
Restrict unauthorized access
This is where token-based authentication systems like JWT became extremely popular.
What Exactly is JWT?
JWT stands for JSON Web Token.
It is a token-based authentication mechanism where the server generates a token after successful login and sends that token to the client. The client then sends the same token with future requests to prove identity.
Instead of storing login sessions on the server side continuously, JWT allows applications to verify users using tokens themselves. This is why JWT authentication is often called stateless authentication because the server does not need to store active login sessions separately for every user.
Understanding Stateless Authentication
In traditional session-based authentication, the server stores user session information internally. Every time the client makes a request, the server checks its stored session data to identify the user.
JWT works differently.
Here, the token itself contains the required user-related information. The client stores the token and sends it along with requests. The server verifies the token and identifies the user from it.
This makes JWT authentication lightweight and scalable for modern APIs and frontend-backend architectures.
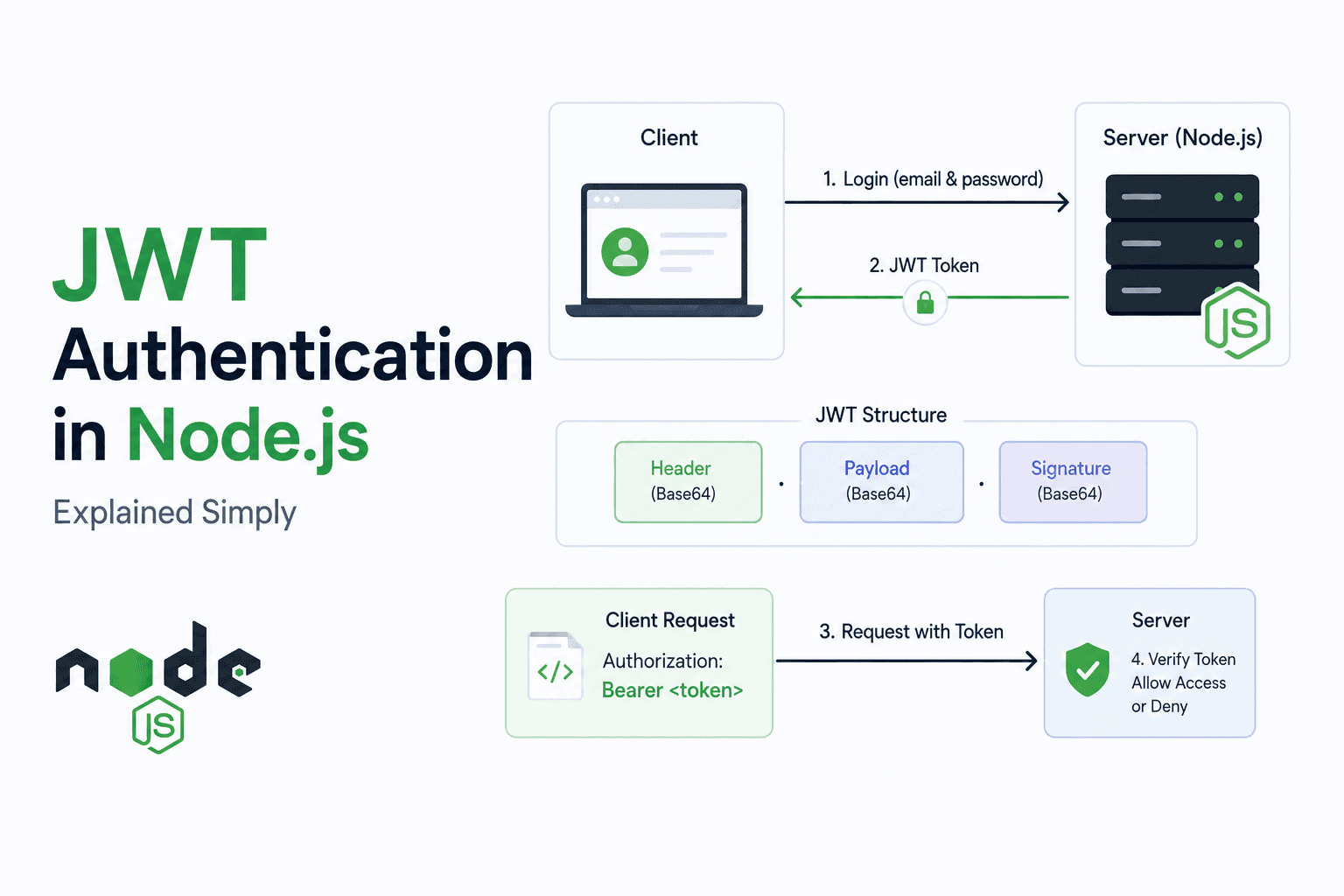
Structure of a JWT
A JWT mainly contains three parts:
Header
Payload
Signature
These three parts are separated using dots.
A JWT looks something like this:
xxxxx.yyyyy.zzzzz
Each part has its own purpose.
Header
The header contains information about the token type and signing algorithm being used.
A very simplified example:
{
"alg": "HS256",
"typ": "JWT"
}
This tells the server what algorithm was used while generating the token.
Payload
The payload contains actual user-related information.
For example:
{
"id": "123",
"email": "user@gmail.com"
}
This data is often called claims. Usually, applications store user IDs, emails, or roles inside the payload.
Signature
The signature is responsible for verifying whether the token was modified or not. It is generated using a secret key on the server side.
You do not need to go deep into cryptography initially. The important thing to understand is that the signature helps maintain token integrity and prevents tampering.
Login Flow Using JWT
Now let’s understand the complete login flow at a high level.
When the user logs in:
Client sends email and password
Server verifies credentials
If credentials are correct, server generates JWT
Token gets sent back to the client
Client stores the token
Client sends the token with future requests
This token becomes the user’s identity proof for protected API access.
Generating JWT in Node.js
To generate JWT in Node.js, applications commonly use the jsonwebtoken package.
Example:
const jwt = require("jsonwebtoken");
const token = jwt.sign(
{ id: 1, email: "user@gmail.com" },
"secretkey",
{ expiresIn: "1h" }
);
console.log(token);
Here:
jwt.sign() creates the token
Payload contains user data
"secretkey" is used for signature generation
expiresIn defines token expiry time
After generation, this token is usually sent back to the frontend.
Sending Token with Requests
Once the client receives the token, it sends the token with future API requests.
Usually, the token is sent inside request headers.
Example:
Authorization: Bearer your_jwt_token
Whenever the backend receives a protected request, it checks whether the token is valid or not before allowing access.
Protecting Routes Using JWT
Now let’s see a very simple protected route example.
const jwt = require("jsonwebtoken");
function verifyToken(req, res, next) {
const token = req.headers.authorization;
if (!token) {
return res.send("Access denied");
}
try {
const verified = jwt.verify(token, "secretkey");
req.user = verified;
next();
} catch {
res.send("Invalid token");
}
}
Here:
jwt.verify() checks token validity
If token is valid, request continues
If token is invalid, access gets denied
This is how protected routes work in JWT authentication systems.
Why JWT Became So Popular
JWT became extremely popular because modern applications often have separate frontend and backend systems. Mobile apps, React frontends, APIs, and microservices all needed a lightweight authentication mechanism that worked well across different platforms.
Since JWT is stateless, scalable, and easy to send with requests, it became a common choice for API-based authentication systems.
Final Thoughts
JWT authentication may initially look slightly complicated because terms like tokens, payloads, headers, signatures, and protected routes appear together. But at its core, the flow is actually very straightforward.
The server verifies user credentials, generates a token, sends it to the client, and later verifies that same token whenever protected resources are accessed.
That is the core idea behind JWT authentication.
Once this flow becomes clear, understanding authentication systems in Node.js becomes much easier because almost every modern backend application eventually uses some form of token-based authentication internally.
Hope it helps!.